The convenience of having all this data at our fingertips is undeniable, it also raises significant security concerns. One wrong move and your confidential information could end up in the wrong hands, leaving you vulnerable to identity theft, financial loss, or even personal harm.
Cornerstone of data protection
At the core of every encrypted note app lies a sophisticated encryption algorithm. This algorithm takes your plaintext notes (the readable information you’ve entered) and transforms them into an unintelligible stream of characters, known as ciphertext. Without the correct decryption key, the ciphertext remains virtually impossible to decipher, effectively rendering your notes useless to anyone who might gain unauthorized access. Most encrypted note apps employ advanced encryption standards (AES) or other industry-recognized algorithms to ensure the highest level of security. Cryptography experts have thoroughly scrutinized and tested these algorithms, and are widely regarded as virtually unbreakable when implemented correctly.
Securing data in transit
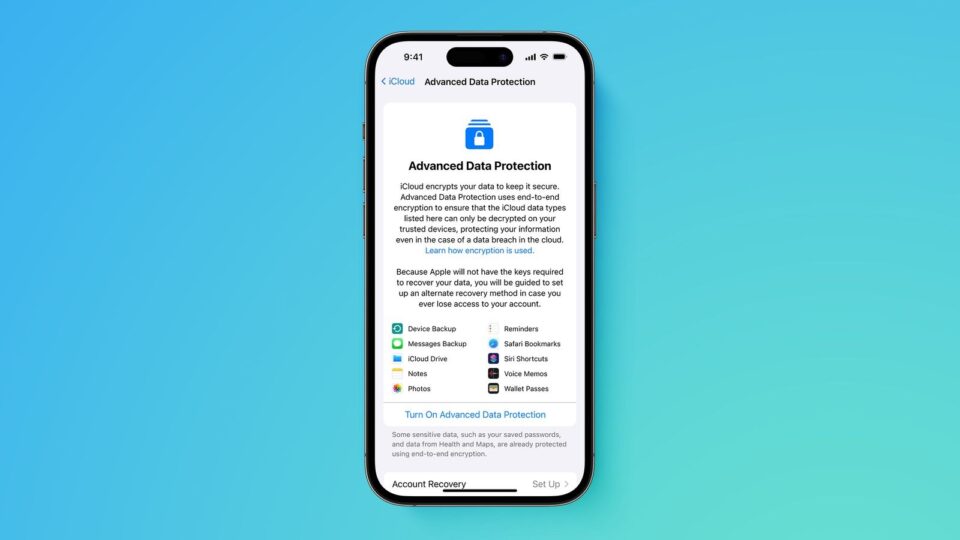
What is a safenote? While encryption is crucial for protecting your notes on your device, it’s equally important to ensure that your data remains secure during transmission. When you sync your encrypted notes across multiple devices or upload them to a cloud storage service, the data travels over the internet, potentially exposing it to interception by third parties. End-to-end encryption ensures that your notes are encrypted on your device before transmission and only decrypted on the receiving end, using the intended recipient’s decryption key. This process prevents anyone in the middle, including the service provider, from accessing your plaintext information. Many reputable encrypted note apps, such as Standard Notes, use end-to-end encryption to safeguard your data during transit, providing an additional layer of security and peace of mind.
Protecting your privacy
Advantage of encrypted note apps is their commitment to preserving your privacy through a zero-knowledge architecture. It means that the app developers and service providers have no way to access or decrypt your notes, even if they want to. With a zero-knowledge architecture, the encryption keys used to secure your data are generated and stored exclusively on your devices. The app developers never have access to these keys, ensuring that your notes remain truly private and secure. Even in the face of legal demands or data breaches, the service provider cannot disclose information they don’t have access to. This approach not only safeguards your privacy but also protects the app developers from potential legal liabilities or coercion to provide user data.
Locking down your notes
To ensure that only authorized individuals access your encrypted notes, most apps employ robust authentication measures.
- Strong password protection – Encrypted note apps often require you to set a strong, unique password to protect your account and notes. Some apps even enforce password complexity requirements to enhance security further.
- Two-factor authentication – Many apps offer an extra layer of security through 2FA, which requires a second form of authentication, such as a one-time code sent to your phone or a biometric element such as fingerprint or facial recognition could be employed.
- Local device authentication – Some apps allow you to secure your notes using your device’s built-in authentication methods, such as a passcode, pattern, or biometric authentication.
By implementing these authentication measures, encrypted note apps ensure that even if someone gains physical access to your device, your notes remain protected and inaccessible without the proper credentials.